Introduction
In a critical development, a critical security imperfection has surfaced in the broadly utilized WordPress plugin Backup Migration,setting more than 50,000 websites in peril of inaccessible code execution. Uncovered by the Nex Group, a collective of watchful bug seekers, the helplessness has been authoritatively assigned as CVE-2023-6553, stamped with a serious rating of 9.8/10.
This article points to dismember the complexities of the recognized powerlessness, explain its potential repercussions, and emphasize the basic require for quick measures to brace websites vulnerable to this security chance.

Background on Backup Migration WordPress Plugin
The Backup Migration plugin for WordPress stands as a significant apparatus within the site administration biological system, bragging a broad client base with over 90,000 installations. Working as an robotization arrangement, the plugin encourages the consistent execution of location reinforcements coordinating them to neighborhood capacity or Google Drive accounts. Its broad appropriation underscores Its noteworthiness in rearranging reinforcement forms for chairmen, advertising comfort and productivity in shielding site information. In any case, later disclosures of a basic security powerlessness, assigned as CVE-2023-6553, have cast a shadow on its unwavering quality, requiring a closer examination of its internal workings and the quick usage of defensive measures to guarantee the astuteness and security of the various websites depending on this plugin.
Purpose and Functionality WordPress
The Purpose and Functionality plugin for WordPress serves as a principal contraption for administrators, advertising an adaptable and streamlined approach to making strides area capabilities. This multifaceted plugin is laid out to move forward and customize particular viewpoints of WordPress, allowing clients to tailor their region to meet particular needs.
From changing client parts and consents to optimizing SEO settings and overseeing security highlights, the Reason and Esteem plugin locks in chairmen with a comprehensive suite of gadgets. Its user-friendly interface ensures accessibility for both amateur and experienced clients, making it a pivotal resource for those looking for a flexible and advantageous induces to maximize the potential of their WordPress websites.
Automating site backups to local storage and Google Drive
The functionality of automating site backups to local storage and Google Drive in WordPress is consistently encouraged through the Reinforcement Movement plugin. This irreplaceable apparatus enables site chairmen to easily plan and execute computerized reinforcements, improving the security and versatility of their destinations.
With the adaptability to select between neighborhood capacity or the comfort of cloud-based capacity on Google Drive, the plugin caters to different client inclinations. By mechanizing this basic viewpoint of site administration, chairmen not as it were guarantee the opportune conservation of their important information but moreover rearrange the reinforcement handle, permitting for a more vigorous and dependable approach to WordPress location support.
Widely adopted with over 90,000 installations
The Backup Migration plugin for WordPress has experienced far reaching selection, outperforming 90,000 establishments and setting up itself as a foundation within the toolkit of many WordPress directors. This significant user base verifies to the plugin’s ubiquity and viability in assembly the basic require for mechanizing location reinforcements.
Its wide acknowledgment underscores the believe put within the plugin by the WordPress community, confirming its unwavering quality in disentangling reinforcement forms and bracing the security of endless websites. The broad utilization of the Reinforcement Relocation plugin highlights its flexibility and commitment to a streamlined and secure site administration encounter for an assorted run of clients.
Discovery of Critical Vulnerability
The basic helplessness in WordPress, distinguished by the Nex Group, underscores the never-ending challenges in keeping up the security of widely used plugins. Found through constant bug chasing, this imperfection has been allowed CVE-2023-6553, carrying a tall seriousness score of 9.8/10.
This disclosure represents the significance of dynamic security observing and the part of careful bug seekers in distinguishing potential dangers. The quick announcement of the powerlessness of WordPress security firm Word fence highlights the collaborative endeavors inside the cybersecurity community to address and correct such basic issues expeditiously.
This occurrence serves as an update of the progressing require for vigorous security hones and persistent observing to protect the endless environment of WordPress websites from potential misuse.
Technical Details of CVE-2023-6553
CVE-2023-6553 represents a critical security vulnerability within the Backup Migration WordPress plugin, found by the Nex Group. This imperfection, evaluated with a seriousness score of 9.8/10, uncovered all plugin adaptations up to and counting Reinforcement Relocation 1.3.6 to potential abuse.
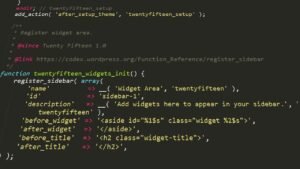
The vulnerability permits unauthenticated aggressors to execute farther code by infusing PHP code through the /includes/backup-heart.php record. The attack vector lies within the plugin’s endeavor to incorporate the bypasser.php record from the BMI_INCLUDES registry, a catalog whose definition, particularly BMI_ROOT_DIR, is subject to client control.
This imperfection empowers danger performing artists to control the values passed to an incorporate work, driving to unauthorized execution of self-assertive code on the influenced server. The revelation of these specialized subtle elements emphasizes the basic nature of the defenselessness, highlighting the require for quick activity to secure vulnerable installations.
Additional WordPress Security Concerns
In addition to the critical vulnerability found in the Backup Migration plugin CVE-2023-6553, there are striking security concerns inside the WordPress biological system. As of late, a Property Situated Programming POP chain defenselessness was tended to by WordPress.
This vulnerability, when exploited under certain conditions, seem possibly permit assailants to execute self-assertive PHP code, especially in multisite establishments and when combined with particular plugins. Whereas the details of this particular defenselessness are not given, the affirmation of such concerns emphasizes the energetic and advancing nature of security challenges within the WordPress stage.

The persistent endeavors to recognize and fix vulnerabilities illustrate the significance of keeping up a proactive security position for site directors and the broader WordPress community. Remaining careful and expeditiously addressing developing security issues is fundamental for guaranteeing the by and large judgment and versatility of WordPress establishments.
Implications for PHP code execution
The implications for PHP code execution in WordPress, especially within the setting of vulnerabilities such as the as of late tended to Property Situated Programming (POP) chain helplessness, are critical. PHP code execution alludes to the capacity of an assailant to run self-assertive PHP code on the server where WordPress is facilitated.
Within the case of vulnerabilities just like the POP chain, aggressors can possibly abuse shortcomings within the PHP code to execute unauthorized commands or control the usefulness of the WordPress location. This postures a serious danger to the security and keenness of the site, as unauthorized PHP code execution can lead to information breaches, unauthorized get to, and other malevolent exercises.
WordPress engineers ceaselessly work to recognize and fix such vulnerabilities to anticipate unauthorized code execution, highlighting the significance of keeping WordPress installations up to date with the most recent security patches and best hones. Site directors must stay careful and proactive in actualizing security measures to relieve the hazard of PHP code execution vulnerabilities.
Conclusion
In conclusion, the critical security vulnerability found within the Backup Migration WordPress plugin, designated as CVE-2023-6553, has raised critical concerns by uncovering over 50,000 websites to the danger of farther code execution.
Discovered by the Nex Group and expeditiously detailed to Wordfence, the seriousness of the blemish underscores the interminable challenges in keeping up the security of widely-used plugins inside the WordPress environment. The specialized subtle elements uncover that unauthenticated assailants can possibly control PHP code through the plugin, posturing an extreme hazard to the influenced websites.
Whereas a fix has been quickly discharged, the determination of helpless establishments emphasizes the direness for directors to upgrade to the secure form, Reinforcement Relocation 1.3.8, or afterward. This occurrence serves as a piercing update of the ever-evolving risk scene within the computerized domain and the basic significance of proactive security measures to defend the judgment and flexibility of WordPress websites.
Site chairmen are encouraged to stay careful, remain informed about security updates, and follow to best hones to brace their advanced resources against potential issues.








